By Derek Hawkins

Sen. Marco Rubio (R-Fla.) on Capitol Hill in Washington on Aug. 2.
Lawmakers are prying into a controversial report that Chinese spies installed surveillance microchips in servers used by Apple, Amazon and other American companies.
On Wednesday, Sens. Marco Rubio (R-Fla.) and Richard Blumenthal (D-Conn.) wrote to Supermicro, the firm that manufactured the compromised hardware, asking whether it had detected any such tampering in its products.
The senators said “the nature of the claims raised alarms that must be comprehensively addressed.”
“We are alarmed by the dangers posed by back doors, and take any claimed threat to the nation’s networks and supply chain seriously,” they said.
“We are alarmed by the dangers posed by back doors, and take any claimed threat to the nation’s networks and supply chain seriously,” they said.
“These new allegations require thorough and urgent investigation for customers, law enforcement and Congress.”
Other lawmakers on the Hill have fired off similar missives.
Other lawmakers on the Hill have fired off similar missives.
Sen. John Thune (R-S.D.) wrote to Apple, Amazon and Supermicro requesting staff briefings about the Bloomberg article by Friday.
And House Oversight Committee Chairman Trey Gowdy (R-S.C.) and Intelligence Committee Chairman Devin Nunes (R-Calif.) called on the heads of the FBI, Department of Homeland Security and the Office of the Director of National Intelligence to provide a classified briefing on the matter by Oct. 22. (Amazon.com founder and chief executive Jeffrey P. Bezos owns The Washington Post.)
The flurry of requests underscores long-standing concerns in Congress about the potential for China to conduct cyber espionage by infiltrating the supply chain.
The flurry of requests underscores long-standing concerns in Congress about the potential for China to conduct cyber espionage by infiltrating the supply chain.
So lawmakers aren’t taking any chances with the allegations raised in it.
“If this news report is accurate, the potential infiltration of Chinese back doors could provide a foothold for adversaries and competitors to engage in commercial espionage and launch destructive cyber attacks,” Rubio and Blumenthal wrote.
“If this news report is accurate, the potential infiltration of Chinese back doors could provide a foothold for adversaries and competitors to engage in commercial espionage and launch destructive cyber attacks,” Rubio and Blumenthal wrote.
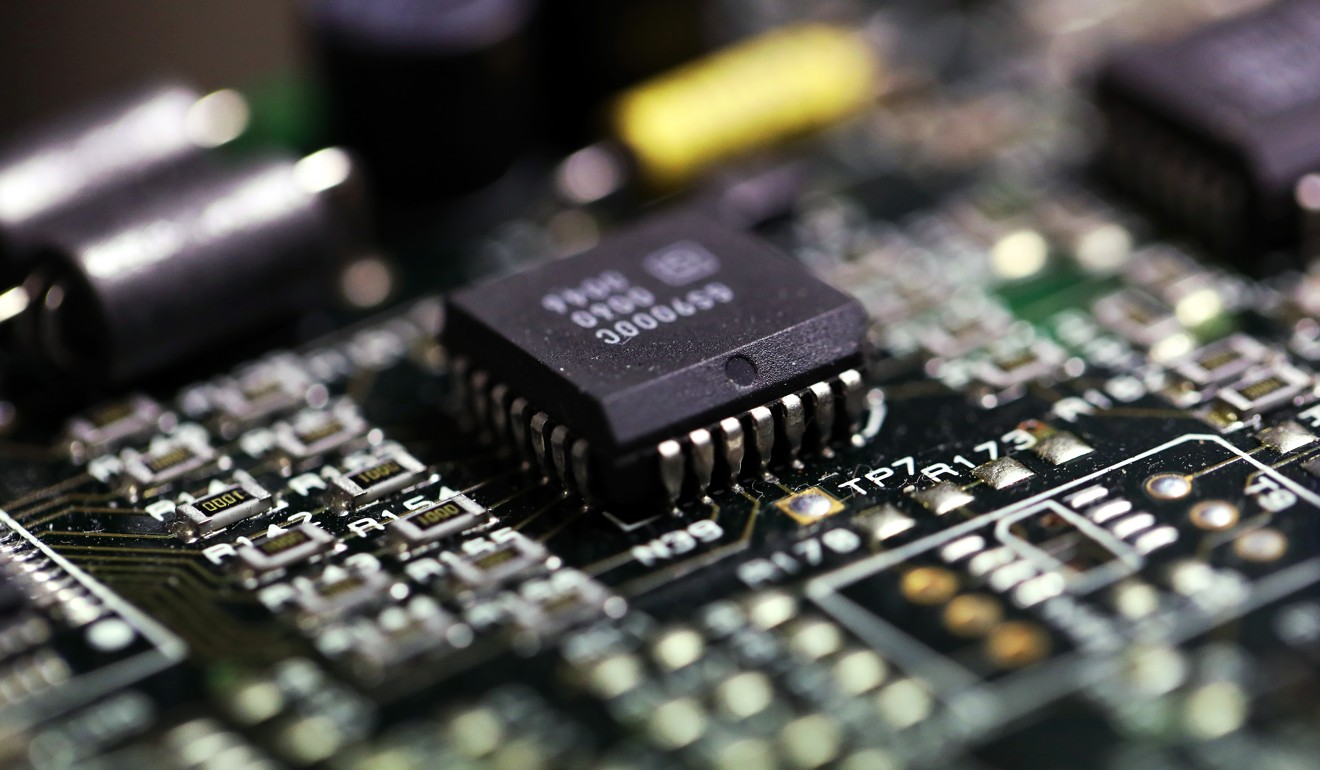
The explosive Bloomberg report said that operatives from a unit of the People’s Liberation Army secretly installed the surveillance chips in Supermicro motherboards during the assembly process in China, creating a “stealth doorway” into networks that used the machines.
Citing unnamed government and corporate officials, the report described it as the “most significant supply chain attack known to have been carried out against American companies.”
Sen. Ron Johnson (R-Wis.), chairman of the Homeland Security Committee, said in a hearing Wednesday morning that he found the story credible.
He asked FBI Director Christopher A. Wray and Homeland Security Secretary Kirstjen Nielsen, who testified in the hearing, whether they were aware of “implantation of chips in the supply chain.”
Wray deflected.
Wray deflected.
“Be careful what you read in this context,” he said, adding that he was barred from commenting on whether the FBI was investigating the matter.
Nielsen said that supply chain hacks are "a very real and emerging threat that we are very concerned about."
Indeed, the article seemed to channel some of Washington’s worst anxieties about supply chain security.
Lawmakers and federal officials have long fretted over whether a foreign adversary could carry out such an infiltration, and over the past year they’ve taken steps to try to prevent it.
Lawmakers and federal officials have long fretted over whether a foreign adversary could carry out such an infiltration, and over the past year they’ve taken steps to try to prevent it.
Last fall, DHS directed federal agencies to stop using software made by the Russian cybersecurity contractor Kaspersky over concerns that Moscow’s intelligence services could use the company to conduct cyber espionage.
Shortly after, Congress banned federal agencies from using Kaspersky’s products as part of the defense spending bill.
Lawmakers and military officials have raised similar fears that Chinese telecom giants ZTE and Huawei could be used as conduits for Beijing to spy on U.S. citizens, companies and government offices.
This year, lawmakers abandoned an effort to prohibit federal agencies and contractors from doing business with ZTE at the request of the White House.
China a bigger security threat than Russia, says FBI Director Wray
Nielsen also warned senators that China “absolutely” is “exerting unprecedented effort to influence American opinion" in her appearance before the Senate Homeland Security and Governmental Affairs Committee on Wednesday.
Nielsen testified alongside Wray and Russell Travers, the acting director of the National Counterterrorism Center at the Office of the Director of National Intelligence.
Asked by Sen. Jon Kyl (R-Ariz.) to assess the risk that Beijing's cyber activities and disinformation efforts represent in comparison to Russia, Wray replied that he was “reluctant to try to rank threats” but added that “China in many ways represents the broadest, most complicated, most long-term counterintelligence threat we face.”
Asked by Sen. Jon Kyl (R-Ariz.) to assess the risk that Beijing's cyber activities and disinformation efforts represent in comparison to Russia, Wray replied that he was “reluctant to try to rank threats” but added that “China in many ways represents the broadest, most complicated, most long-term counterintelligence threat we face.”
Wray told Kyl that China will remain a threat to the United States in the long run.
“Russia is in many ways fighting to stay relevant after the fall of the Soviet Union. They're fighting today's fight,” Wray said.
“China is fighting tomorrow's fight, and the day after tomorrow, and the day after that. And it affects every sector of our economy, every state in the country and just about every aspect of what we hold dear.”


 Chinese mole or Trojan horse: Charles Liang opened gates to Chinese intelligence services.
Chinese mole or Trojan horse: Charles Liang opened gates to Chinese intelligence services.